Security researchers often refer to security, and especially computer and device security, as a race. A race between people just trying to go about their daily business, and those that would rather steal their money than earn it. As engineers and researchers find new and better ways to protect people from thieves and scammers, the thieves and scammers are finding new and creative ways to defeat those measures.
PayJunction helps merchants pull ahead of malicious actors in the security race by making the Smart Terminal as secure as possible. In fact, some of the most common scams simply won't work with a Smart Terminal due to the way it is tied in with our secure cloud infrastructure! Replace the Smart Terminal with another terminal that looks the same? It won't work with our Virtual Terminal web portal nor any 3rd party software designed to use the PayJunction Smart Terminal. Wipe out the software on the Smart Terminal and load up a malicious application? Our secure cloud won't accept connections from it any more.
Why You Still Need a Device Security Policy
First, it's required under the PCI-DSS which all businesses must follow in order to process payments on all major payment card brands. That alone mandates that your business have a device security policy.
Next, it's important to note that there are ways to compromise a device before any security technology can protect you and the card holder. A common example is the use of "credit card skimmers" which criminals install in front of the actual credit card reader. The victim believes they are swiping or inserting their card like normal, however the card is passing through two readers: the one placed in front by the scammer, and then the merchant's actual reader. Since the transaction appears to take place as normal, no one is the wiser until suspicious charges start showing up on the card holders account, sometimes weeks later. This type of fraud is most commonly seen on ATMs and other non-attended payment devices such as gas station terminals.
Finally, security only works well when the end user engages it effectively. You could buy the best door and lock in the world, but it's not going to keep someone out if you don't make sure it latches and locks. Having a device security policy and enforcing it is the equivalent of making sure the door is closed and locked behind you.
PCI Requirements
- 9.9 Examine documented policies and procedures to verify they include:
- Maintaining a list of devices.
- Periodically inspecting devices to look for tampering or substitution.
- Training personnel to be aware of suspicious behavior and to report tampering or substitution of devices.
- 9.9.2.a Examine documented procedures to verify processes are defined to include the following:
- Procedures for inspecting devices.
- Frequency of inspections.
- 9.9.3.a Review training materials for personnel at point-of-sale locations to verify it includes training in the following:
- Verifying the identity of any third-party persons claiming to be repair or maintenance personnel, prior to granting them access to modify or troubleshoot devices.
- Not to install, replace, or return devices without verification.
- Being aware of suspicious behavior around devices (for example, attempts by unknown persons to unplug or open devices).
- Reporting suspicious behavior and indications of device tampering or substitution to appropriate personnel (for example, to a manager or security officer).
Recommended Policies and Procedures
Maintaining a List of Devices
A list of Smart Terminals should include the following:
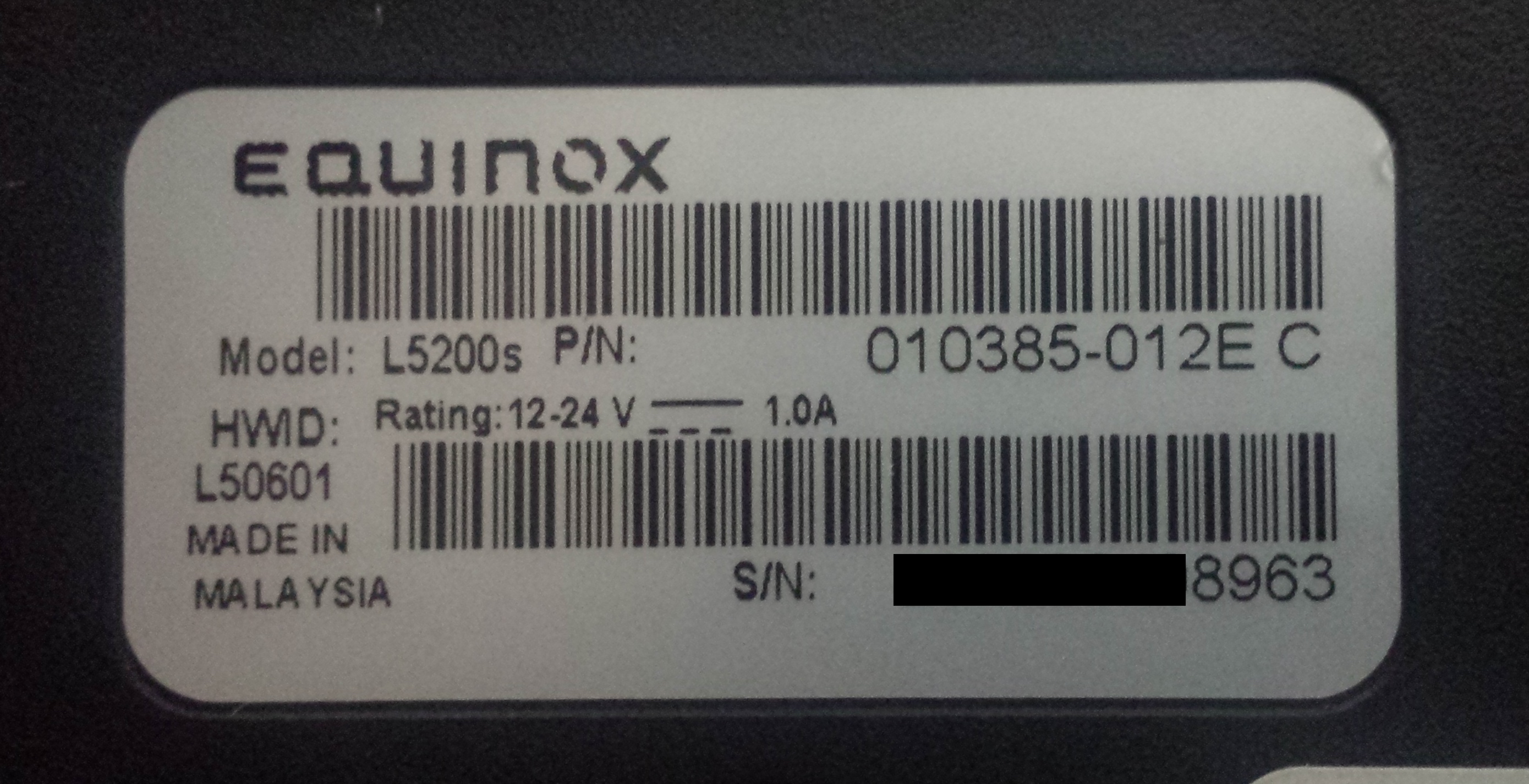
- Serial Number
- Location
- Model
- Notes
- Notes might include distinguishing characteristics, planned changes, etc.
Periodically inspecting devices to look for tampering or substitution
Signs of Tampering
- Scratches on the plastic housing, particularly near seams, recesses, and connection ports
- Objects attached to the device, particularly in front or behind the card swiper and the slot for dipping the chip cards
- Items plugged into ports on the device
It is important to keep in mind that computer devices, particularly USB thumb drives, are smaller than ever:
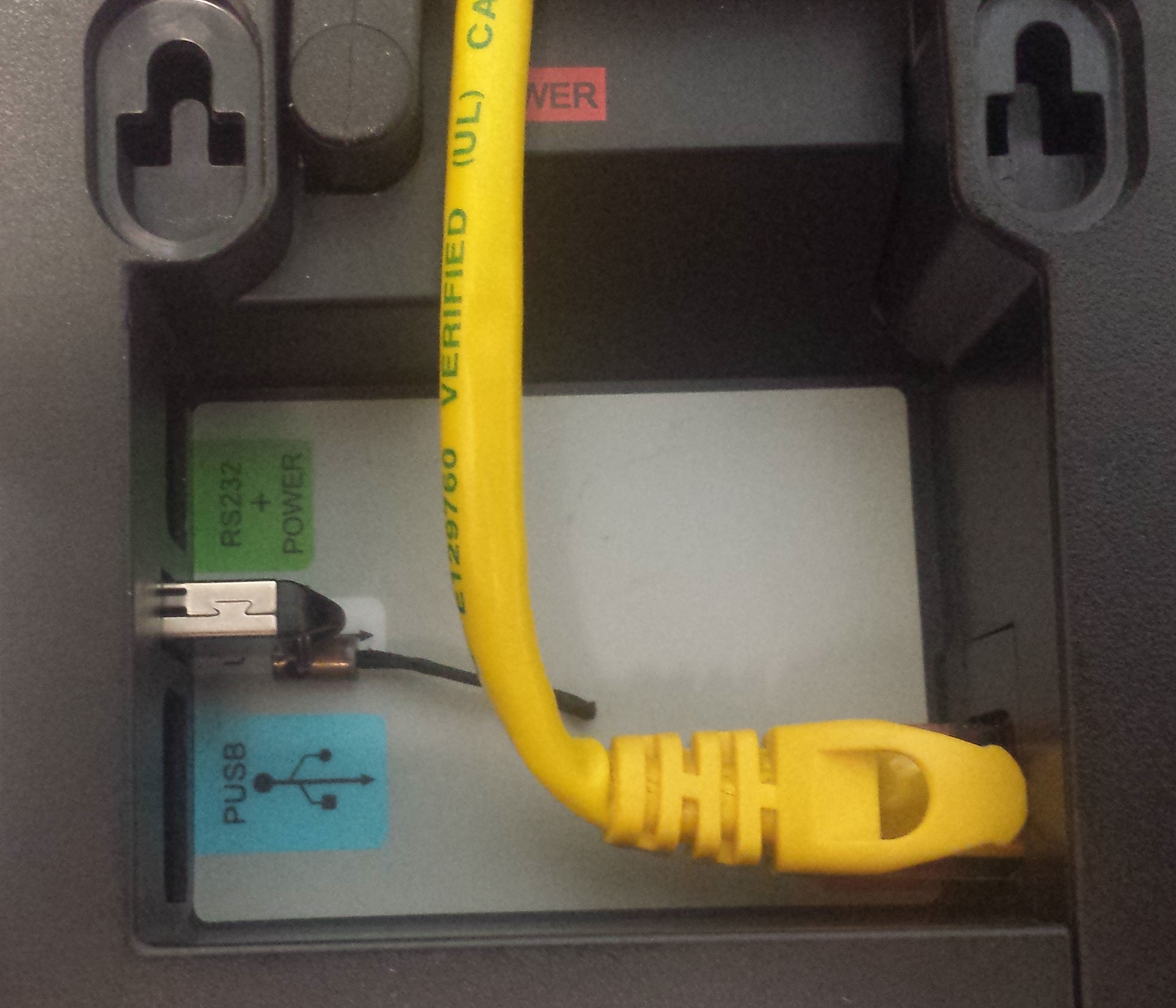
Other than the power cable and the network (Ethernet/CAT5) cable, no other devices or cables should be plugged into any of the ports on the Smart Terminal.
Signs of Substitution
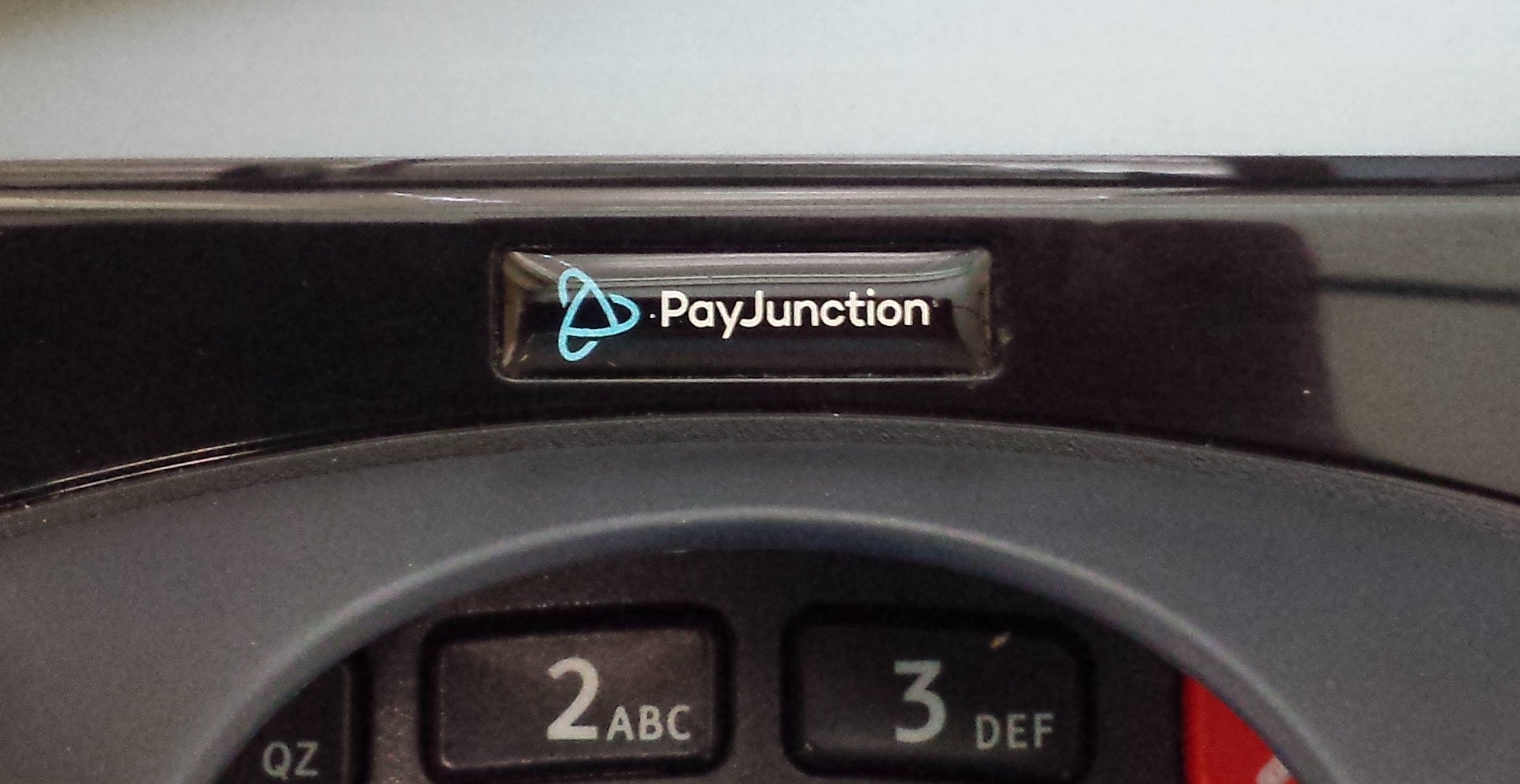
- The PayJunction logo missing from the front of the device, directly above the keyboard:
- A different serial number listed on the metal plate on the bottom of the Smart Terminal device, or something covering the metal plate to hide it:
Procedures for Inspecting Smart Terminals
Inspection procedures should include the following:
- Inspecting the exterior of the Smart Terminal for possible tampering or substitution as outlined above.
- Detaching the Smart Terminal from the stand and inspecting the bottom of the unit to look for additional cables or devices plugged into the ports located here.
Frequency of Inspections
It is recommended to perform inspection procedures at the beginning and end of each shift, as well as after breaks or long periods when the Smart Terminal was not under observation.
Training for Employees
All employees whom can grant access to the Smart Terminal should be trained to:
- Verify the identity of any third-party persons claiming to be repair or maintenance personnel
- At the time of writing this article, PayJunction does not contract any third party persons, companies or service providers to perform repair or maintenance on Smart Terminal hardware. Any technician would be employed by the merchant themselves and should be verified with the office manager or business owner.
- Any caller claiming to be from PayJunction and asking for either changes to be made, or information on the Smart Terminal should be verified. Requested information might include, but is not limited to, the serial number of the unit, it's specific model, the MAC address, or IP address.
- To verify a caller is from PayJunction, the recommended procedure is to get the name and extension of the caller, then call them back at PayJunction's 1-800 number. The current number can always be viewed by logging into PayJunction by hovering your mouse over the Account button at the bottom left of each page:
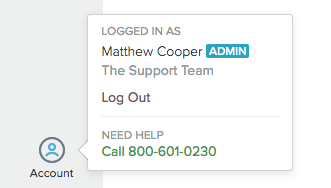
- CallerID can be easily faked by knowledgable scammers and should not be considered proof of a caller's identity
- To verify a caller is from PayJunction, the recommended procedure is to get the name and extension of the caller, then call them back at PayJunction's 1-800 number. The current number can always be viewed by logging into PayJunction by hovering your mouse over the Account button at the bottom left of each page:
- Not to install, replace, or return devices without verification.
- PayJunction will not send new units or accessories unannounced. Any replacement terminal or accessories received without prior arrangement with PayJunction support personnel should be questioned and verified.
- Being aware of suspicious behavior around devices
- There is no need for a customer or stranger to remove the Smart Terminal from it's stand or to plug anything but their card into the appropriate slot on the device, at any time. Attempts to remove the Smart Terminal from its stand, turn it over, or plug anything into the device should be viewed with suspicion and reported.
- Reporting suspicious behavior
- Information found on the bottom of the unit, including the serial number and MAC address, can be used by social engineers to trick a merchant into reducing their security to allow attackers to remotely attack the device. Employees should report if someone is caught looking at this information and should be on the lookout for unsolicited calls regarding the device as they may be social engineering attacks. See above for instructions on verifying a caller is from PayJunction.
- The unit should always be inspected immediately after observing suspicious behavior.
Training Should be Periodic and Ongoing
Do you remember everything you were taught on the first day of the job? Don't let security be something forgotten: training should occur at least annually if not more frequently.
The Security Race Never Ends
We're all part of the security ecosystem in the modern age of computers. Employees should never have the mindset that an electronic device is "un-hackable". An "un-breakable" door and "un-pickable" lock can be defeated by preventing the door from latching. Ask yourself and your employees, how would you feel if another merchant allowed your card information to be stolen? How likely would you be to do business with that merchant again? Competition is tough enough in the modern age without losing the trust of your customers, and some businesses are never able to recover from a major security breach.
Is the Smart Terminal built for security? Yes. Does PayJunction keep refining the Smart Terminal technology to make it more secure as time goes on? Absolutely. However, the race goes on, and will continue to go on, so long as there are those willing to scam and steal for a living.